Zero Trust for Distributed Teams: Securing Access Without a Perimeter
Traditional perimeter security assumes everyone inside the network is trusted. Distributed teams have no perimeter. Zero trust verifies every access request regardless of location.
Marcus Sterling
January 31, 2026
The traditional network security model drew a clear line between trusted and untrusted: inside the corporate network was trusted, outside was not. Firewalls enforced this boundary, VPNs extended it to remote workers, and once authenticated, users had broad access to network resources. This model assumed that threats came from outside and that internal network traffic was inherently safe.
Distributed teams shatter this assumption. When employees work from homes in Temecula, coffee shops in Encinitas, coworking spaces in downtown Los Angeles, and client sites across Orange County, there is no meaningful network perimeter to defend. Every access request originates from an untrusted network, and the concept of inside versus outside loses all meaning. Zero trust architecture acknowledges this reality by treating every access request as potentially hostile, regardless of its origin.
Core Zero Trust Principles
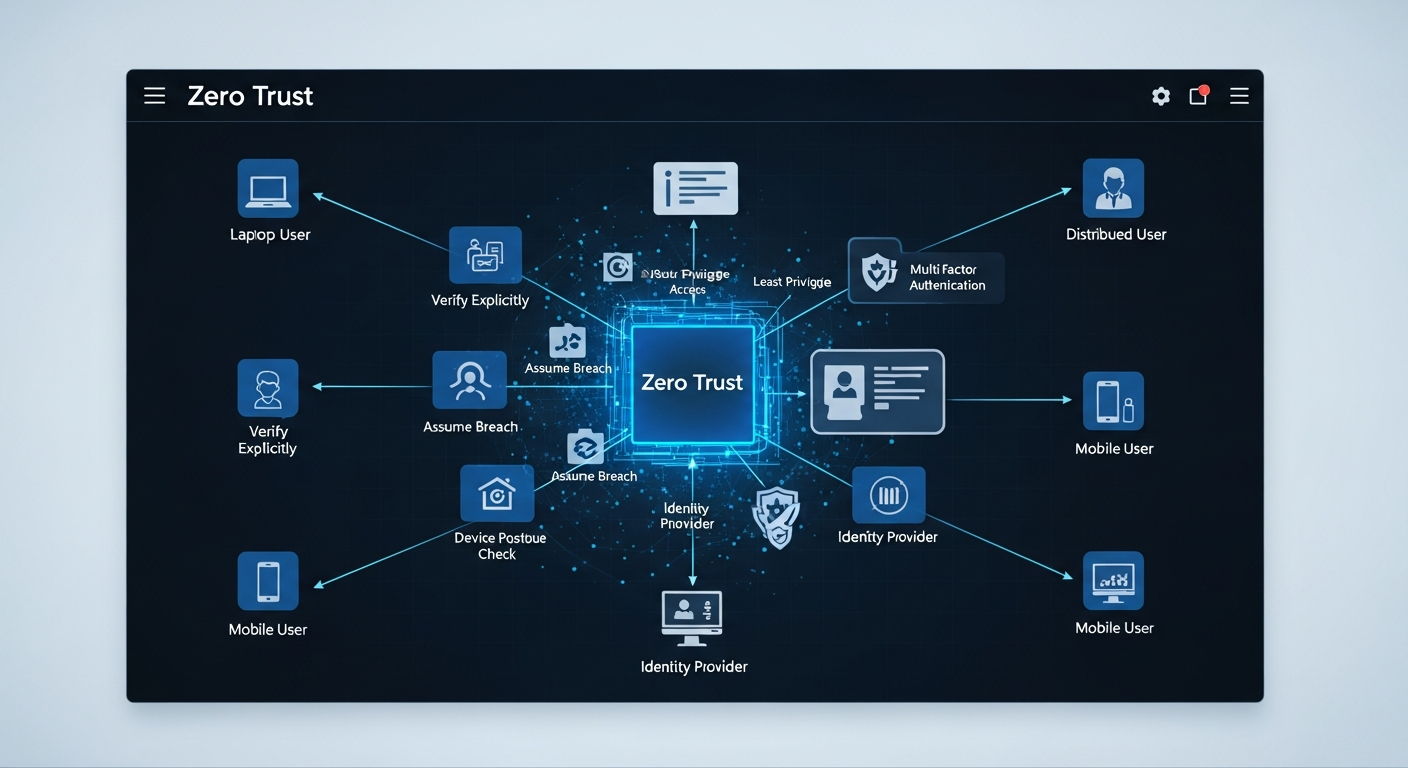
Zero trust operates on three core principles: verify explicitly, use least privilege access, and assume breach. Verify explicitly means that every access request is authenticated and authorized based on all available data points, including user identity, device health, location, time of day, and the sensitivity of the resource being accessed. Least privilege means granting only the minimum access necessary for the specific task. Assume breach means designing systems so that a compromised account or device cannot laterally move to access additional resources.
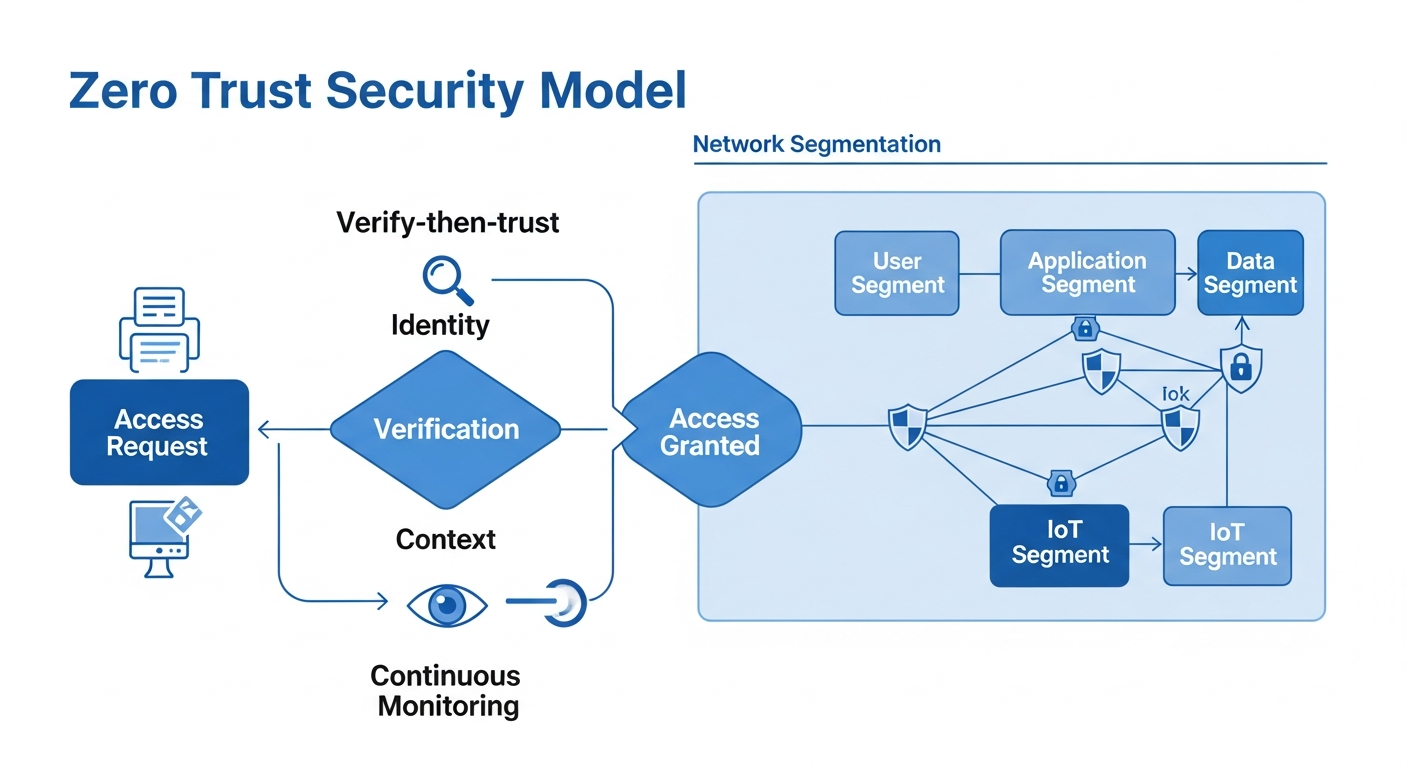
Implementation starts with identity. Multi-factor authentication is the foundation of zero trust, ensuring that stolen passwords alone are insufficient for access. Device health checks verify that endpoints meet security requirements, including current operating systems, active endpoint protection, and encrypted storage, before granting access. Micro-segmentation limits lateral movement by restricting communication between network segments to only approved traffic patterns.
Implementing zero trust across our distributed team of 120 employees in eight Southern California locations was transformative. We eliminated our VPN infrastructure entirely and reduced our attack surface by over 70 percent. Every access request is now evaluated individually.
— CTO, distributed SoCal technology company
Zero Trust Implementation with BlueHouse
BlueHouse Telecom designs and implements zero trust architectures for Southern California businesses with distributed teams. We integrate identity management, device health verification, and micro-segmentation into a comprehensive security framework. Contact us to begin your zero trust journey.
Protect Your Business Today
Cyber threats are evolving faster than most businesses can keep up. Schedule a free security assessment with our team to identify vulnerabilities and build a defense strategy tailored to your organization.