VPN vs. SASE: Choosing the Right Secure Access Model for Your Business
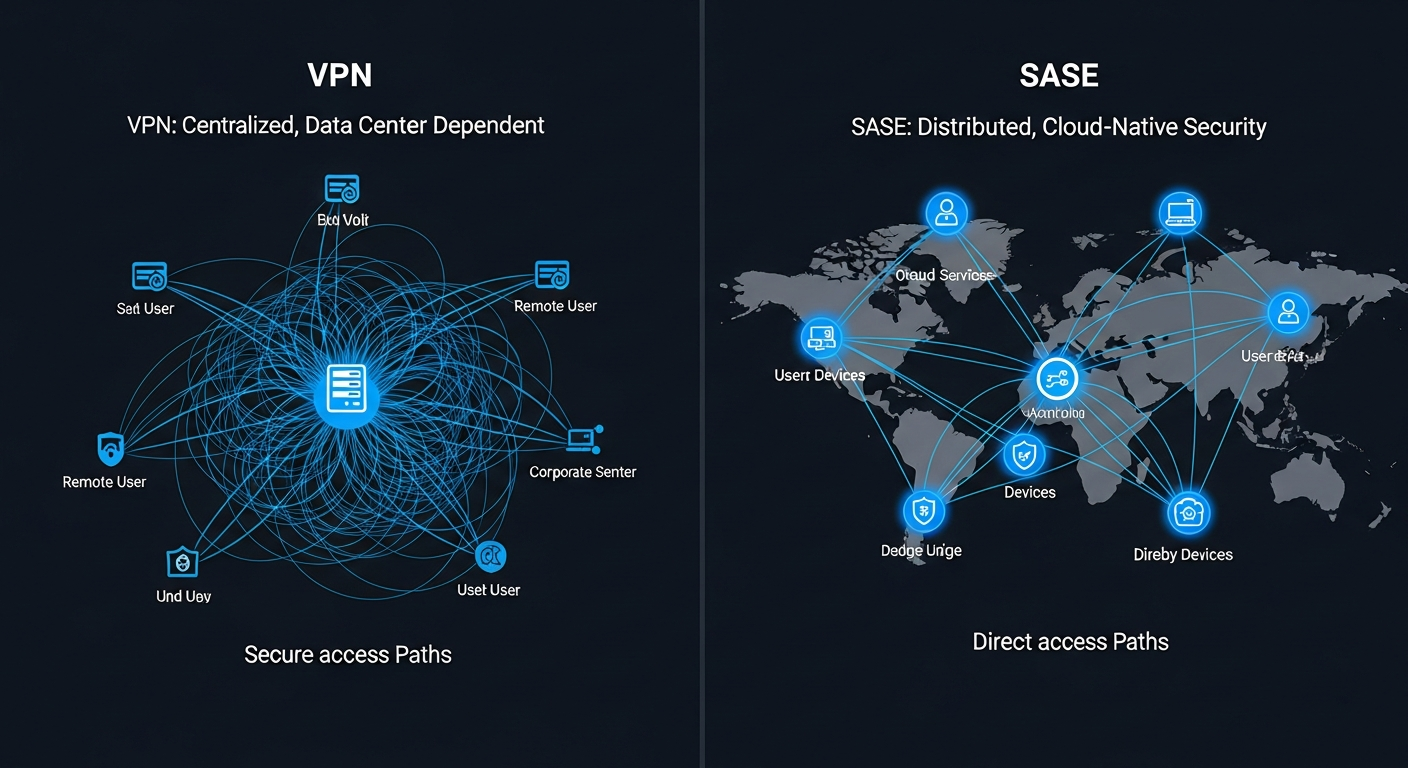
Traditional VPNs backhaul all remote traffic through your headquarters, creating bottlenecks and single points of failure. SASE provides direct, secure cloud access from any location.
Elias Thorne
January 15, 2026
Virtual private networks have been the standard remote access solution for decades, creating encrypted tunnels between remote employees and the corporate network. The model worked well when most applications lived on servers in your San Diego or Los Angeles headquarters and remote work was the exception rather than the norm. But the shift to cloud-based applications and distributed workforces has exposed fundamental limitations in the VPN architecture.
When a remote employee in Temecula connects to a VPN at your Irvine headquarters to access a cloud application hosted in a data center in Virginia, their traffic travels from Temecula to Irvine and then from Irvine to Virginia, doubling the network distance and adding latency at the VPN concentrator. Multiply this by 50 or 100 simultaneous remote users and the VPN becomes a bottleneck that degrades performance for everyone.
How SASE Changes the Architecture
Secure Access Service Edge, or SASE, replaces the centralized VPN model with a distributed, cloud-native security architecture. Instead of routing all traffic through your headquarters, SASE applies security policies at the nearest cloud point of presence. A remote employee in Temecula connects to a local SASE node that applies your security policies, inspects traffic for threats, and routes the connection directly to the cloud application without any detour through headquarters.

The security model also improves with SASE. Traditional VPNs provide network-level access: once connected, the remote user has broad access to network resources. SASE implements zero-trust principles by evaluating every access request individually based on user identity, device health, location, and the specific resource being accessed. This granular approach limits the blast radius if a remote device is compromised.
Our VPN was the number one complaint from remote employees across our four Southern California offices. After moving to SASE, application performance for remote workers improved by 60 percent and we eliminated the VPN concentrator as a single point of failure.
— VP of Technology, multi-location SoCal accounting firm
SASE Solutions from BlueHouse Telecom
BlueHouse Telecom designs and deploys SASE architectures for Southern California businesses transitioning from legacy VPN infrastructure. We evaluate your application portfolio, user distribution, and security requirements to determine whether VPN, SASE, or a hybrid approach is the right fit. Contact us for a secure access architecture consultation.
Protect Your Business Today
Cyber threats are evolving faster than most businesses can keep up. Schedule a free security assessment with our team to identify vulnerabilities and build a defense strategy tailored to your organization.