Anatomy of a Data Breach: Lessons from Real Southern California Incidents
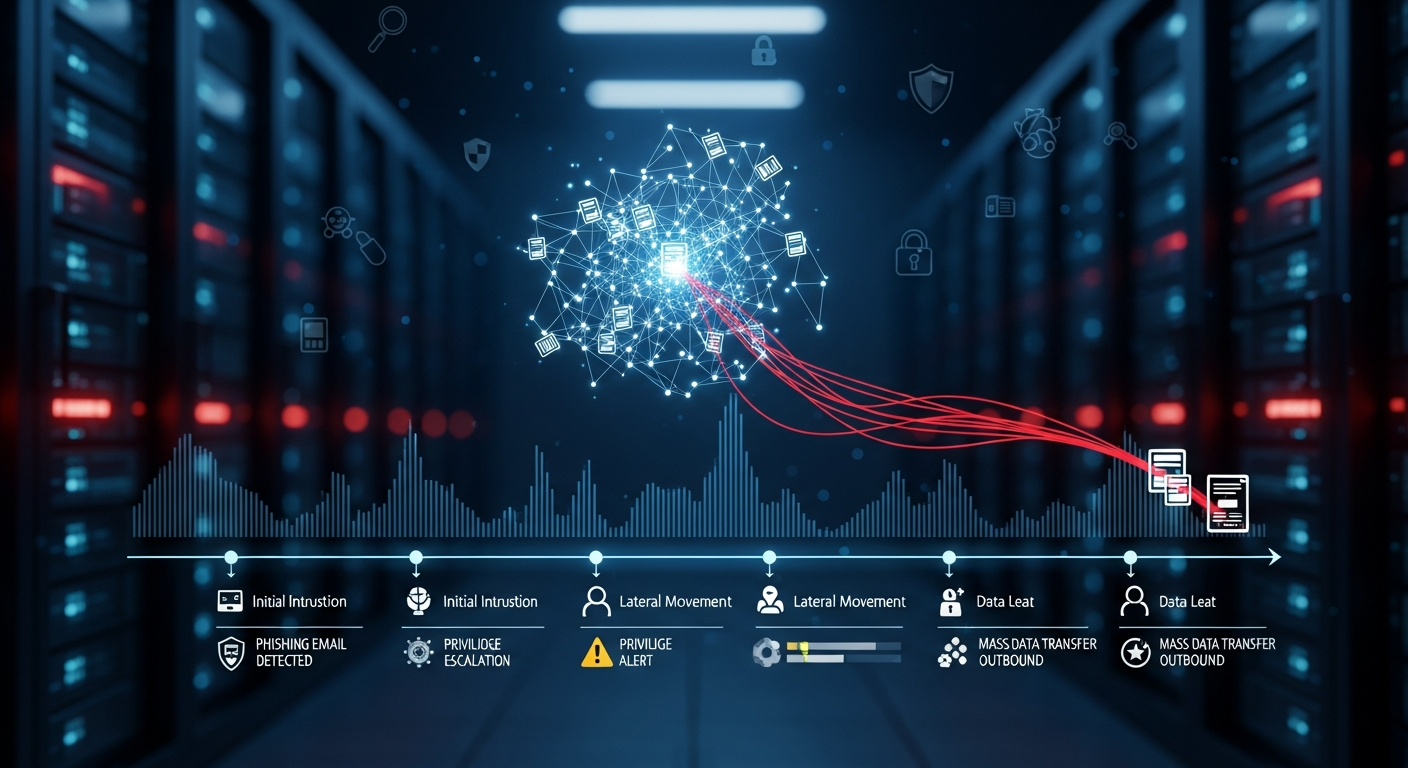
Data breaches do not happen overnight. They follow predictable patterns that, once understood, reveal opportunities to detect and stop attacks before they cause damage.
Marcus Sterling
December 4, 2025
In the past 18 months, BlueHouse has assisted multiple Southern California businesses in responding to and recovering from data breaches. While the specific details are confidential, the patterns are consistent enough that every business owner in San Diego, Orange County, and the Inland Empire should understand how these attacks unfold. Data breaches are not random lightning strikes. They follow a predictable sequence of stages, and at each stage there are opportunities to detect and stop the attack before it achieves its objective.
The typical breach we encounter in the Southern California mid-market follows a pattern that security researchers call the kill chain. It begins with reconnaissance, where the attacker gathers information about the target from public sources. It progresses through initial compromise, usually via phishing or exploitation of an unpatched system. The attacker then moves laterally through the network, escalating privileges until they reach the data or systems they want to access.
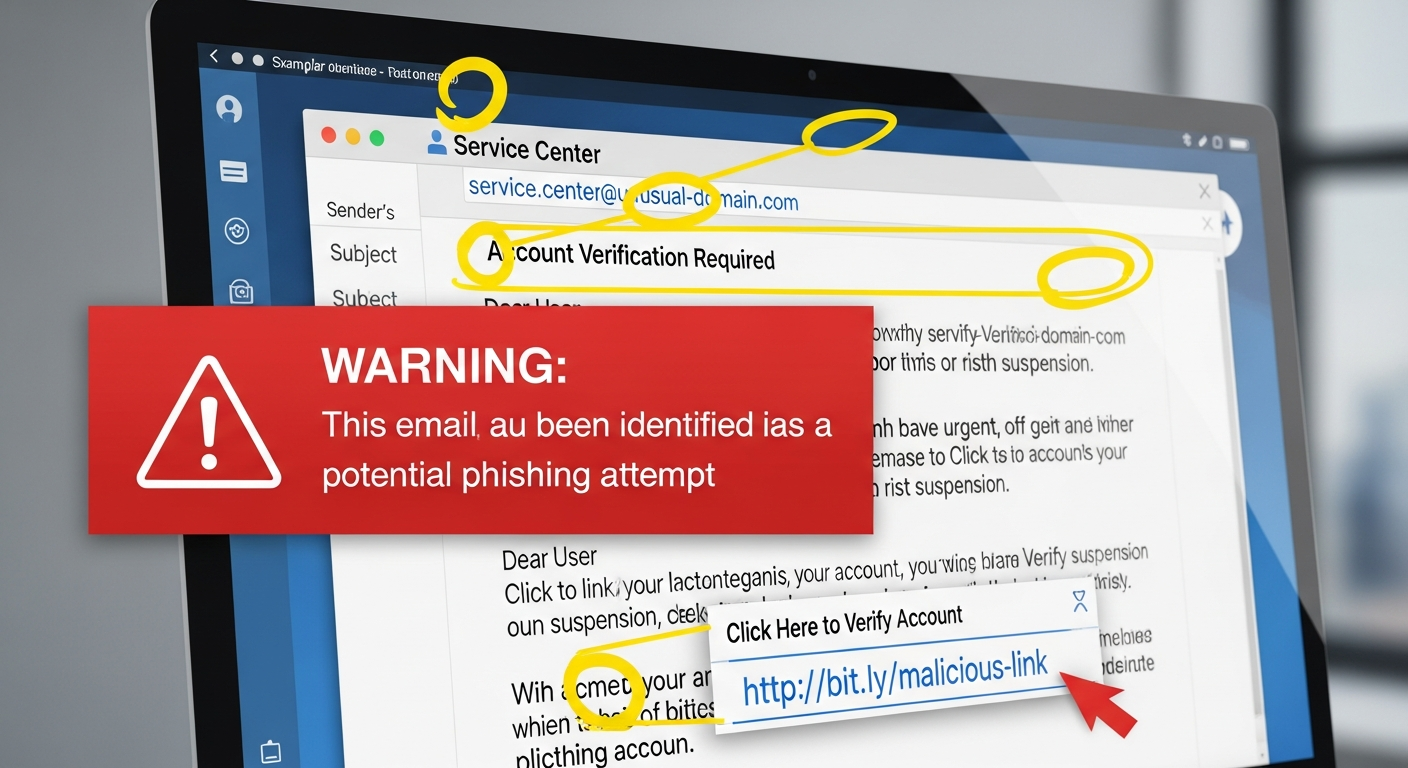
Stage One: The Initial Compromise
In every breach we have investigated, the initial compromise was preventable. Phishing emails that tricked employees into entering credentials on fake login pages were the most common entry point. In several cases, the phishing emails were highly targeted, referencing specific projects or internal terminology that the attacker had gathered from LinkedIn profiles and company websites. Multi-factor authentication would have prevented all of these initial compromises, regardless of how convincing the phishing email appeared.
The attacker was inside our network for 47 days before we detected them. In that time, they had mapped our entire file structure and identified every database containing customer information.
— IT Director, San Diego professional services firm (anonymized)
Detection and Response: Where Seconds Matter
The average time from initial compromise to detection in the United States is over 200 days, according to IBM's annual Cost of a Data Breach report. Every day an attacker spends inside a network increases the damage and the cost of remediation. The businesses that fare best are those with active monitoring, endpoint detection, and incident response plans that enable rapid containment. BlueHouse's managed cybersecurity service includes 24/7 monitoring and a median detection time of under four hours for anomalous activity on managed networks.
If your Southern California business has not conducted a security assessment in the past year, you may already be compromised and not know it. BlueHouse offers comprehensive security assessments that evaluate your current posture, identify vulnerabilities, and test your incident response readiness. The cost of an assessment is a fraction of the cost of a breach, and the peace of mind it provides is invaluable.
Protect Your Business Today
Cyber threats are evolving faster than most businesses can keep up. Schedule a free security assessment with our team to identify vulnerabilities and build a defense strategy tailored to your organization.